Mesh and Hub-and-Spoke Networks on Azure: Architectural Considerations for Virtual Network Peering
We are excited to announce the availability of a new whitepaper (https://aka.ms/HubAndSpoke) that addresses scalable networking architecture design in Azure. In this paper, we focus on two networking topologies: Mesh network architecture and hub-and-spoke network architecture.
In this whitepaper, we look into these two main network topologies used by Azure customers. We discuss their applications in designing typical Line of Business (LoB) topologies (shown below), M&A networking topologies and Blockchains networking topologies. We highlight some of their scalability limitations and showcase how to work with the current Azure networking limits. We also discuss how to design these topologies using Azure Virtual Network Peering (VNet Peering).
[caption id="attachment_1505" align="alignright" width="451"]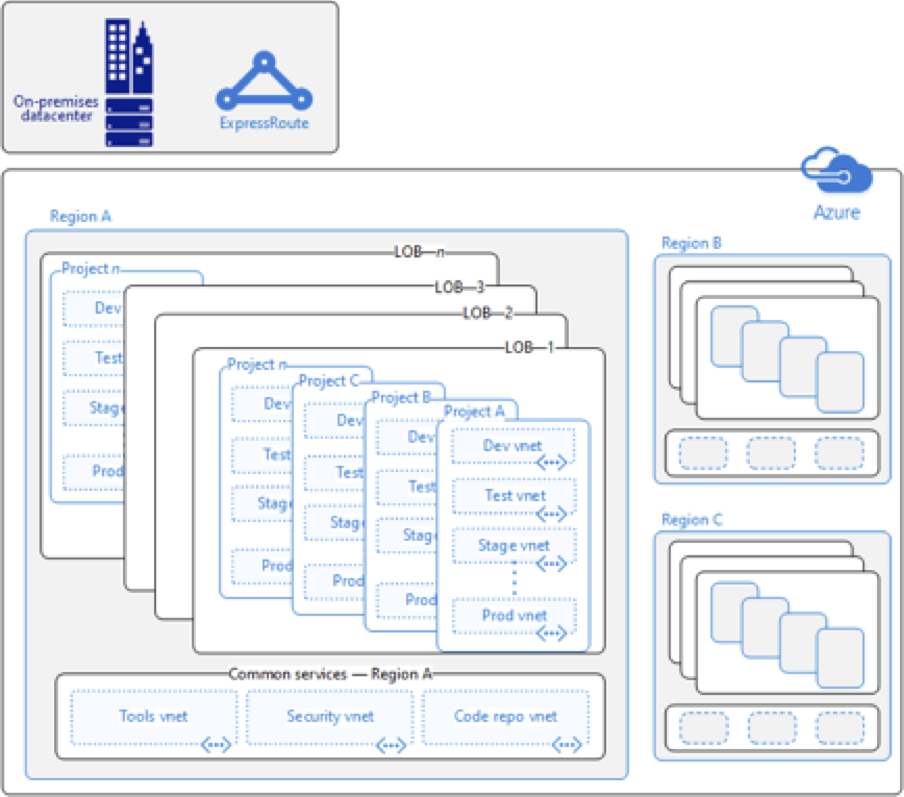 Typical LOB enterprise network configuration with Express Route connection to on-premises datacenter.[/caption]
Typical LOB enterprise network configuration with Express Route connection to on-premises datacenter.[/caption]
We are seeing a growing number of enterprises use VNet Peering to provide connected, secure workspaces for their business units. Virtual Networks (the peers) are directly linked to each other using private IP addresses. The result is a low-latency, high bandwidth connection using the Microsoft backbone without the use of virtual private networks or gateways. VNet Peering gives Azure customers a way to provide managed access to Azure for multiple line-of-business (LOB) teams or to merge teams from different companies altogether. But as enterprises expand their networks, they may encounter subscription limits, such as the default limit for maximum number of peering links. Most of these limits can be increased through a support request. hub-and-spoke network architecture can provide an alternative architecture to provide scalability beyond the VNet Peering subscription limits.
In this whitepaper, we showcase how customers design their enterprise mesh networks and hub-and-spoke networks, and show how enterprises work with, or around, the default maximum number of peering links. In addition, we describe the pros and cons of the two designs and some insights into controlling access through policy and roles.
We hope you find this whitepaper useful.