How to troubleshoot IE Enhanced Security warning "Content from the website listed below is being blocked by the Internet Explorer Enhanced Security Configuration" ?
Hello Everyone!
This is Vinod from the IE team and I would like to share an informative concept about the IE Enhanced security feature which I discovered.
Scenario: User of a Terminal Server, still getting a Warning even after the administrator disabled it via Server Manager or Script.
In the Terminal Server environment we have a concept called Terminal Services Shadowing.
On a terminal server, whenever applications are installed, it first writes the new application registry entries to the HKEY_CURRENT_USER\Software registry location. At the same time, to ensure that these new entries are available for all the users on the terminal server, the new registry entries are propagated to another location in the registry called the shadow region:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Terminal Server\Install\Software
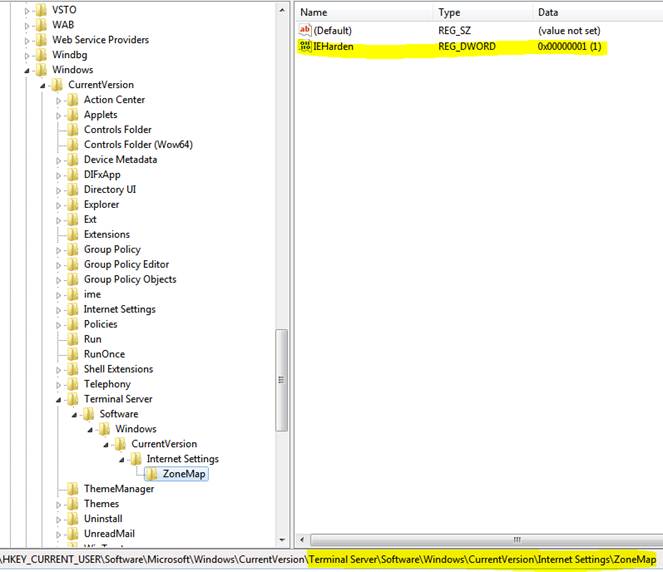
So when we initially built the Terminal servers the IE Enhanced security feature creates a registry key under:
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Terminal Server\Install\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap] – IEHarden
If you turn off the IE Enhanced Security from the UI or run the batch file, it will remove the settings from various other locations but not from the Shadow region.
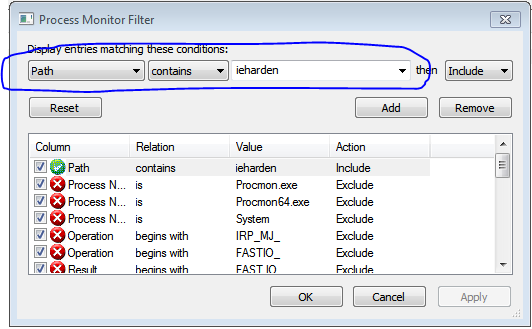
How to troubleshoot IE Enhanced Security prompt issues?
You might get various symptoms like the once below:
- In 2003 and 2008 servers both the admin and the users are prompted with IE enhanced security even when the feature is Turned Off
- Users are being prompted for credentials while accessing their internal website.
- After adding a site to the Local Intranet Zone through group policy, the site continues to load under the Trusted Sites Zone
- Unable to run add-ons when IE is launched as a RemoteApp on the Windows 2008 R2 terminal server
Sample prompts that we can get:
"Content from the website listed below is being blocked by the Internet Explorer Enhanced Security Configuration".
"This Website uses a data provider that may be unsafe"
In all these scenarios if it is a Terminal server and if you have enabled shadowing, it is worth to verify whether the issue is actually caused by IE enhanced security or not.
The value for IEHarden will be set to 1 if the symptoms are being caused by IE Enhanced Security.
This will be a good start for troubleshooting to isolate if the issue is happening because of IE Enhanced security or not.
Note: The update batch file is available from the following blog article ">How to disable IE Enhanced Security on Windows 2003 & Windows 2008 Server silently?"
Regards,
The IE Support Team