How to bypass the security warning "Unknown Publisher" with the checkbox "Always Ask Before Opening this File"
Hi everyone!
Axel here from the IE Escalation team with a scenario related to Security Warning - Unknown Publisher pop-up when executing a file that came from a non trusted source.
| Please note: The example below sets HIGH RISK files types to LOW RISK so that they can be executed without having to honor the warning dialog. We are creating this example because many corporate customers request this change to make their day-to-day operations easier to maintain. With that said, setting these options in attachment manager can put your system at risk, so please fully read the external documentation available on Attachment Manager and weigh the risks involved before making the decision to allow these files types to be executed without warning the user. |
I am sharing this out because the immediate assumption is that by just adding the server name to the Local or Trusted Site zone will allow the file to be executed, which is not accurate. Once the file comes down from the untrusted source and with the Block file stream (see Fig. 1.1), until you remove the attribute you wont be able to run it without first getting the warning mentioned in this blog, see fig. 1.0.
Fig. 1.0 [Screenshot of the Warning with the checkbox “Always ask before opening this file” option] 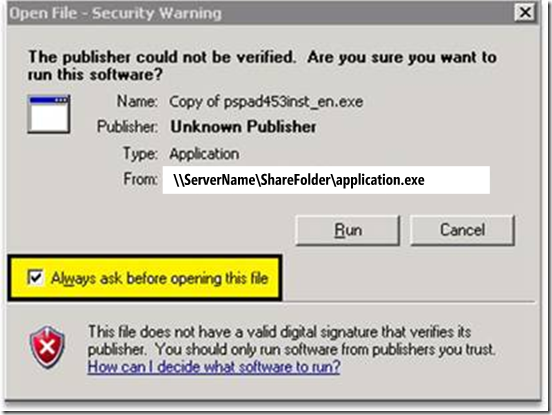
Fig. 1.1 [Screenshot of the executable properties, showing the Security Unblock option] 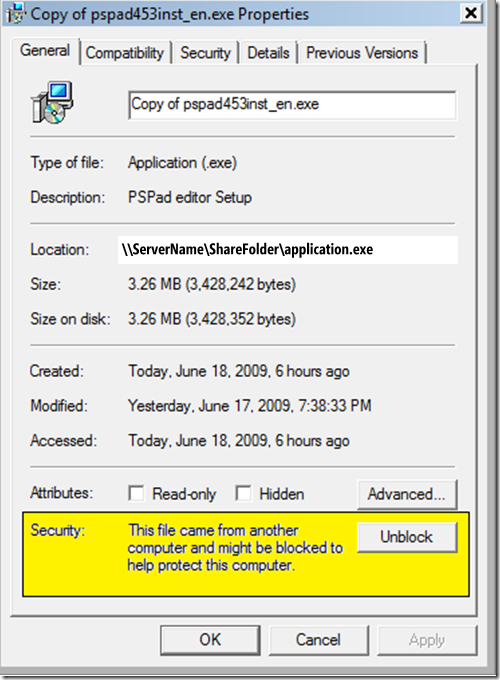
Here is what it may look like once you have unchecked the option next to “Always ask before opening this file”.
Fig. 1.2 [Here is what you will still get, even after you have removed the checkbox] 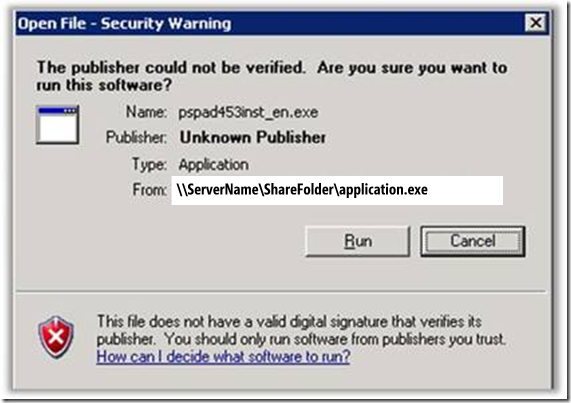
Once you add the unc path to either the Local or Trusted Sites Zone, you will no longer get the warning.
In the above example, we can see that the application did not have a digital signature that verifies its publisher, so we will have to do more work to bypass the warning. You can either have the executable signed using signcode.exe or use the Build in Windows Attachment Manager Policy.
The reason why you get the warning in the first place is because in Windows XP/SP2 and Windows 2003/SP1 we have introduced a new feature called Attachment Manager. This feature was added to help protect your computer from unsafe file attachments. This include accessing files across your network (e.g \\servername\share), files that you might receive with an e-mail message and from unsafe files that you might save from the Internet.
If the Attachment Manager identifies an attachment that might be unsafe, the Attachment Manager prevents you from opening the file, or it warns you before you open the file.
Here are the steps to bypass the warning using Attachment Manager Group Policy. I am also including the registry key modified by the policy.
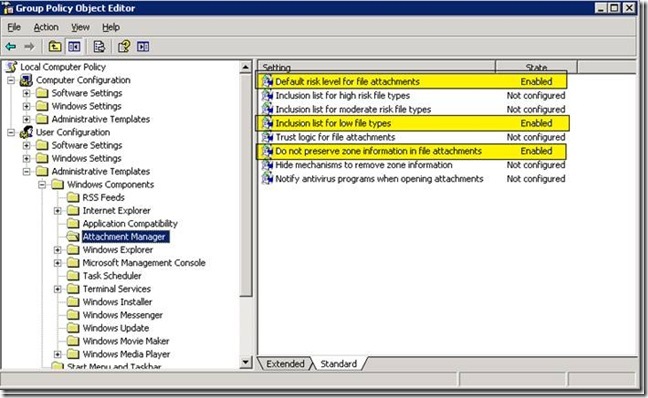
From Start Run type: gpedit.msc
From User Configuration> Administrative Template> Windows Components> Attachment Manager
Set the following:
Configuration Settings:
- Default risk level for file attachments: Set it to Enabled and Set the default risk level to[Low Risk]
- Inclusion list for low file types: Set it to Enabled and add the file extension [.exe;.vbs;.msi]
- Do not preserve zone information in file attachments: Set it to Enabled.
Close Gpedit.msc and run gpupdate /force
Final Step:
- Add the UNC to Local Intranet or Trusted Sites
- Log off and log back in
- Test accessing the UNC share
Registry keys:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies]
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations]
"LowRiskFileTypes"=".exe;.vbs;.msi"
"DefaultFileTypeRisk"=dword:00001808
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments]
"SaveZoneInformation"=dword:00000001
Article below explains everything about Attachment Management.
- 883260 Description of how the Attachment Manager works in Windows XP Service Pack 2 https://support.microsoft.com/default.aspx?scid=kb;EN-US;883260
- How would you sign your file. You could use signcode.exe from Microsoft. Here is also an article:
- Steps for signing a .cab file: https://support.microsoft.com/default.aspx?scid=kb;en-us;247257
Regards,
The IE Support Team