Microsoft Dynamics CRM 2011 log-in issue due to AD FS Certificate Rollover
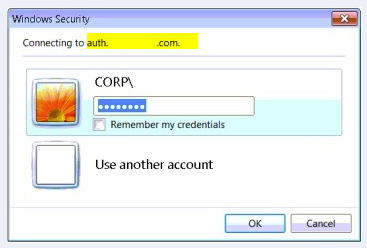
Recently, we came across an interesting issue where in without changing anything in CRM server or ADFS server , authentication starts failing for all users . Every time when we try to access CRM external URL or CRM internal URL we get prompted continuously for URL https://<auth.domain.com>.
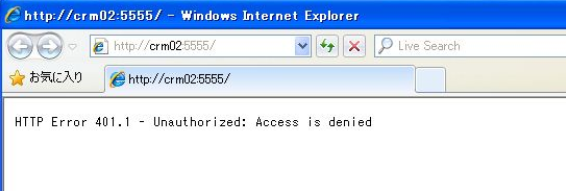
Once we enter our credentials we receive following error :-
HTTP Error 401 - Unauthorized Access is denied.
An error has occurred.
We receive following error in event viewer of ADFS server (Application and Services Logs -> ADFS 2.0 -> Admin ) :-
Exception information:
Exception type: SecurityTokenException
Exception
message: ID4175: The issuer of the security token was not recognized by the IssuerNameRegistry. To accept security tokens from this issuer, configure the IssuerNameRegistry to return a valid name for this issuer.
at Microsoft.IdentityModel.Tokens.Saml11.Saml11SecurityTokenHandler.CreateClaims(SamlSecurityToken samlSecurityToken)
at Microsoft.IdentityModel.Tokens.Saml11.Saml11SecurityTokenHandler.ValidateToken(SecurityToken token)
at Microsoft.IdentityModel.Tokens.SecurityTokenHandlerCollection.ValidateToken(SecurityToken token)
at Microsoft.IdentityModel.Web.TokenReceiver.AuthenticateToken(SecurityToken token, Boolean ensureBearerToken, String endpointUri)
at Microsoft.IdentityModel.Web.WSFederationAuthenticationModule.SignInWithResponseMessage(HttpRequest request)
at Microsoft.IdentityModel.Web.WSFederationAuthenticationModule.OnAuthenticateRequest(Object sender, EventArgs args)
at Microsoft.Crm.Authentication.Claims.CrmFederatedAuthenticationModule.OnAuthenticateRequest(Object sender, EventArgs args)
at System.Web.HttpApplication.SyncEventExecutionStep.System.Web.HttpApplication.IExecutionStep.Execute()
at System.Web.HttpApplication.ExecuteStep(IExecutionStep step, Boolean& completedSynchronously)
OR
Encountered error during federation passive request.
Additional Data
Exception details:
Microsoft.IdentityServer.Web.AuthenticationFailedException: ID3034: Authentication failed.
at Microsoft.IdentityServer.Web.FederationPassiveAuthentication.SubmitRequest(MSISRequestSecurityToken request)
at Microsoft.IdentityServer.Web.FederationPassiveAuthentication.RequestBearerToken(MSISSignInRequestMessage signInRequest, SecurityTokenElement onBehalfOf, SecurityToken primaryAuthToken, String desiredTokenType, Uri& replyTo)
at Microsoft.IdentityServer.Web.FederationPassiveAuthentication.BuildSignInResponseCoreWithSecurityToken(SecurityToken securityToken, WSFederationMessage incomingMessage)
at Microsoft.IdentityServer.Web.FederationPassiveAuthentication.BuildSignInResponseForProtocolRequest(FederationPassiveContext federationPassiveContext, SecurityToken securityToken)
at Microsoft.IdentityServer.Web.FederationPassiveAuthentication.BuildSignInResponse(SecurityToken securityToken)
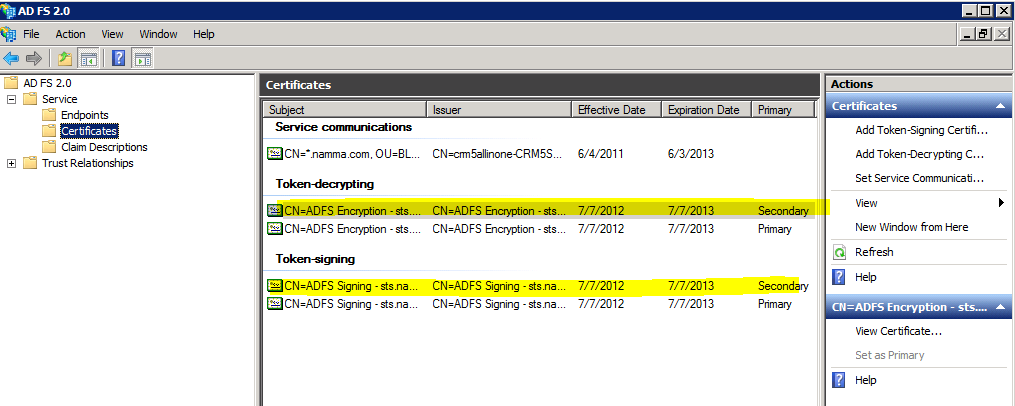
The signing certificate in AD FS shows two Token-decrypting and Token-signing certificates with one Primary and one Secondary status:-
As you can see, there are two signing certificates, the second signing certificate was created by AD FS automatically because the first signing certificate was reaching it's expiration date. This feature - AD FS creating a new self-signed certificate when the old one nears expiration - is called Auto Certificate Rollover.
In the CRM server database it still has the old certificate entry and hence the authentication starts failing. The issue will get resolved once the database gets updated with new values after we re-configure.
Cause
The Token-signing certificate and Token-Decrypting certificate in ADFS gets automatically renewed by AD FS , by Auto Certificate Rollover feature because these certificates reached their expiration date. This feature - AD FS creating a new self-signed certificate when the old one nears expiration - is called Auto Certificate Rollover.
Resolution
In ADFS management Console update the Federation metadata URLs and do an IIS reset on CRM server. Next, restart the ADFS service.
If above steps do not resolve the issue please follow below steps:-
1) In CRM server go to Deployment Manager and then disable the Claims Based Authentication.
2) Do an IISReset on CRM server
3) Re-configure Claims- Based Authentication from Deployment manager keeping all the settings same.
4) Re-configure IFD through deployment manager.
5) Do an IISRESET again on CRM server
6) In ADFS management console in ADFS server , update the corresponding Federation
Metadata URLs.