AddInSpy - Diagnosing/Troubleshooting Office Add-ins
AddInSpy is a new diagnostic tool for reporting the maximum possible information about all Office add-ins registered on a machine. This is a free (unsupported) download, available on MSDN Code Gallery here. Covering article on MSDN here.
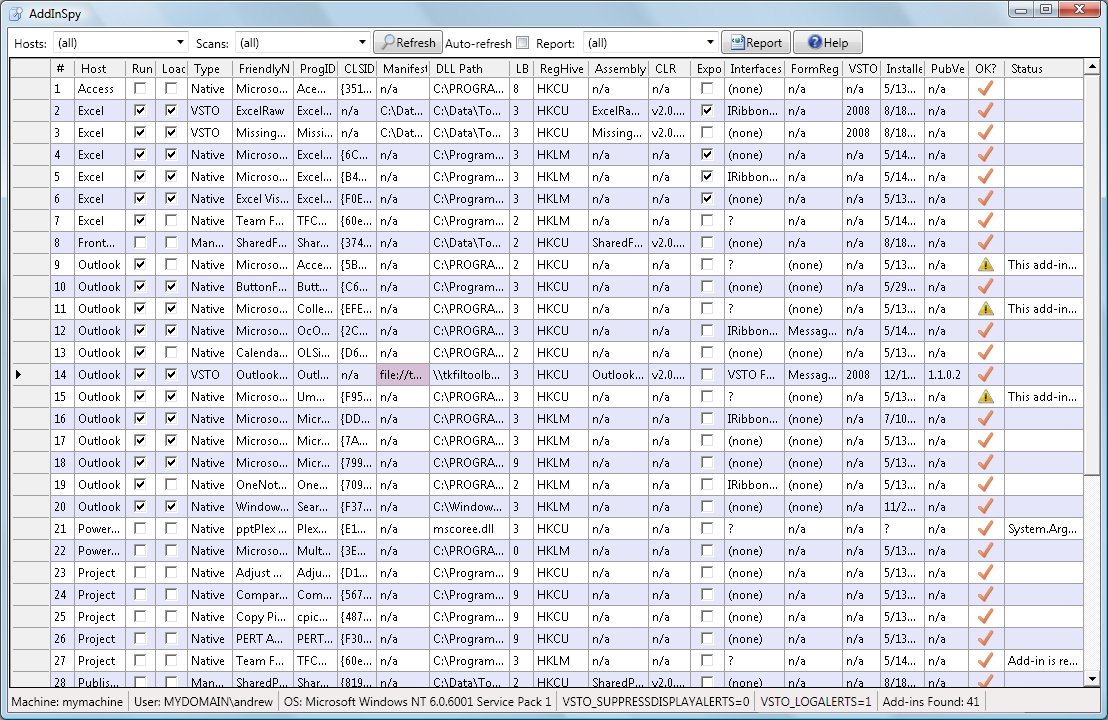
In fact, there are 2 tools: AddInSpy, which is a WPF GUI application, and AS, which is a scriptable console application. They both use the same scanning engine, so results are identical. Both tools allow you to produce an XML report of add-ins, and AddInSpy additionally displays the scan results in a convenient grid.
The tool discovers and reports a lot more information than is available through the Office UI natively, and will report on all registered add-ins, for all Office client applications that support COM add-ins, that is: Access, Excel, FrontPage, InfoPath, Outlook, PowerPoint, Project, Publisher, SharePoint Designer, Visio and Word. The tool covers native add-ins, managed shared add-ins and VSTO add-ins. It does not report on other extensions (Smart Tags, automation add-ins, and the like). The reported information includes the following:
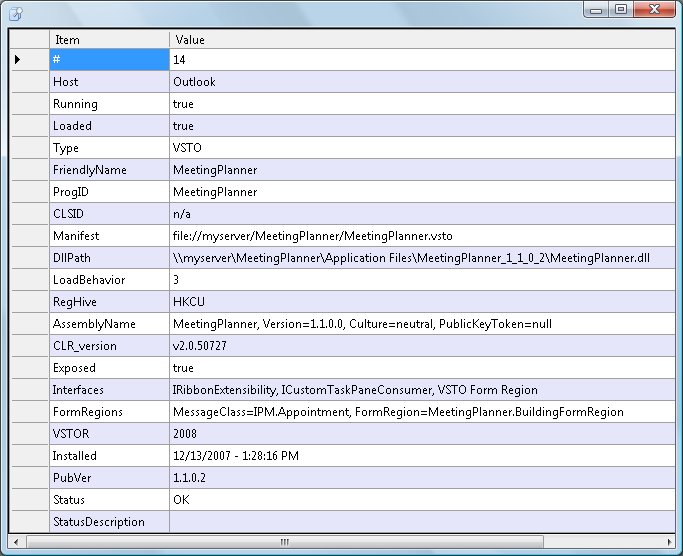
ú The type of each add-in: VSTO, managed non-VSTO, native.
ú FriendlyName, ProgID, CLSID and LoadBehavior of the add-in.
ú For managed add-ins, the manifest path, assembly path, and assembly strongname, and the CLR version the add-in was built against.
ú The registry hive (HKCU or HKLM) where the add-in is registered.
ú For VSTO add-ins, the VSTO runtime version used by the add-in.
ú Installed date, and publish version, where applicable.
ú Which extensibility interfaces the add-in implements (IRibbonExtensibility, ICustomTaskPaneConsumer, FormRegionStartup, IBlogExtensibility, IBlogPictureExtensibility, EncryptionProvider, SignatureProvider or IDocumentInspector).
ú Whether the add-in uses any of the VSTO wrappers for Ribbon, custom taskpane, or custom form region.
ú Whether the add-in exposes itself for automation through the COMAddIns collection of the host application.
ú Whether the host application is running, and whether the add-in is loaded.
ú Whether the add-in is in the disabled items list (aka “blacklist”) for the current user, for each selected Office host application.
ú Context information: machine name, user/domain name, OS details, VSTO environment variables.
Both AddInSpy and AS support comprehensive configuration, allowing you to specify what type of scan to perform, and what types of data to include in the report. AddInSpy reports are configurable via the UI, whereas AS reports are configurable via command-line switches. Here’s a screenshot of the main AddInSpy window (made small so it fits on this blog):
You can also drill down on individual add-ins if you want, and get a dialog with the data for just one add-in of interest:
Note: this tool is a work in progress. Please download it, use it, and send me feedback. You can provide feedback (and report any bugs) on the Code Gallery site for the tool, or by posting comments to this blog post. Give it a work-out, and let me know what you think.