Who Access My File?
In my post File Access Auditing - I Am Not Afraid Of GPO I've digested technet documentation on how to set Active Directory Group Policy Object (AD GP) to enable file access auditing as security measure to prevent repudiation. It is heavy weight techniques for scenarios where developer just needs to understand why she gets "Access denied" during development or while deploying in test environment - "Strange, it all worked on my machine...." :)
For that purpose I use two light weight tools from Sysinternals, the whole portal of Sysinternal's tools is here Windows Sysinternals loaded with free goodies.
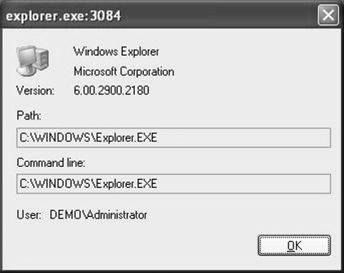
First tool is file monitor (filemon) - it monitors file access activity and when double clicking on some line it shows the user accessed that file:
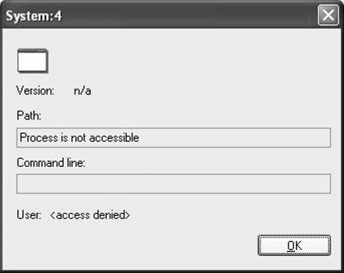
But when the file is accessed from other machine, filemon does not have this information:
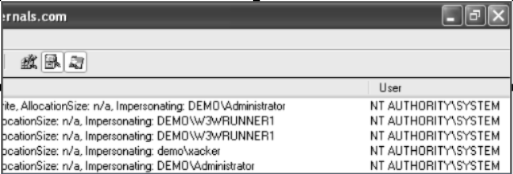
Mark Russinovich kindly explained me why it is not there and suggested using another great tool - process monitor. The tool has details column which includes the data what I was looking for - Impersonating:<<account name>>:
Very cool, very usable, very light weight
Enjoy