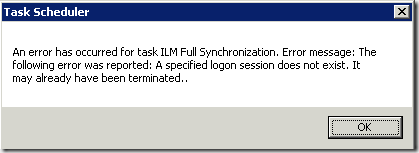
Task Scheduler – A Specified Logon Session Does Not Exist
If you get this error when attempting to create a scheduled task:
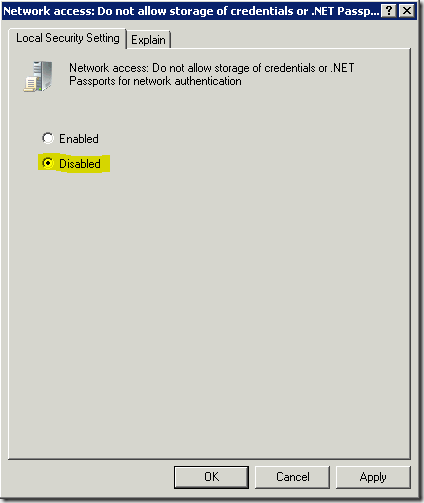
Then check to make sure that your “Local Security Policy” (under Security Settings – Local Policies – Security Options), “Network access: Do not allow storage of credentials or .NET Passports for network authentication” is Disabled:
I’ve now been bitten twice by this, and it’s time to get it down for posterity.